Threat Exposure Management: mnemonic’s recommendations for 2026
Traditional proactive security models based on scheduled scans and compliance-driven patching cannot keep pace with today's threat landscape

Written by:

TL;DR
Organisations are facing a rapidly expanding threat landscape, with more vulnerabilities disclosed each year, faster exploitation timelines, and security teams struggling to prioritise risks across a growing number of tools. This development has sparked the growth of new concepts, methodologies, and security solutions, making it increasingly difficult to keep track of everything.
In this blog post, we first explore the current threat landscape, looking at it mainly from an exposure and vulnerability perspective. Then we provide some guidance and general recommendations by outlining the current key methodologies and solutions within Threat Exposure Management (TEM) and the field of proactive security in general. The challenge, at its core, comes down to two critical areas:
- identifying exposures and vulnerabilities
- validating and prioritising findings to focus on what truly matters
Finally, the blog post will include some key vulnerability and exposure statistics that mnemonic has seen from our customers during the year 2025.
The challenge
Organisations are no longer only defending their internal networks, but are now also managing risks from cloud services, third-party providers, vulnerable identities, and dark web exposures. The traditional security model based on scheduled scans and compliance-driven patching cannot keep pace with this development.
At the same time, security teams are overwhelmed by alerts and other reports from a growing number of tools and monitoring solutions. This creates cybersecurity fatigue, and the volume of findings makes it difficult to focus on the most important threats and exposures. As a result, actual critical issues often remain unaddressed, while time is spent investigating less relevant areas.
These challenges highlight the need for a more structured approach to threat exposure management. Organisations must consolidate visibility, prioritise findings more effectively, and adopt a proactive security mindset. This helps security teams focus on the exposures that truly matter while reducing operational noise and cybersecurity fatigue.
Today's threat landscape: Vulnerabilities and exposures
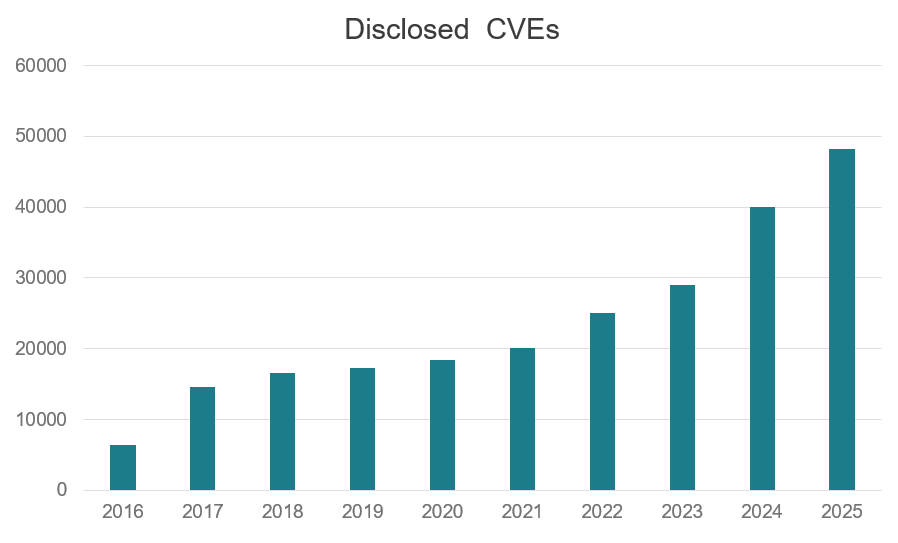
Today’s threat landscape is defined by a rapid growth of the number of discovered vulnerabilities, while at the same time malicious actors increasingly leverage emerging technologies such as AI automation and large language models to exploit new zero-days faster than ever before. This highlights the need for continuous monitoring, especially of externally facing assets, and for effective detection of shadow IT to maintain full visibility and control. In 2025 alone, more than 48,000 new software vulnerabilities (CVEs) were registered, up 20 percent from 2024 and 750 percent in the last 10 years.
(source: cve.org)
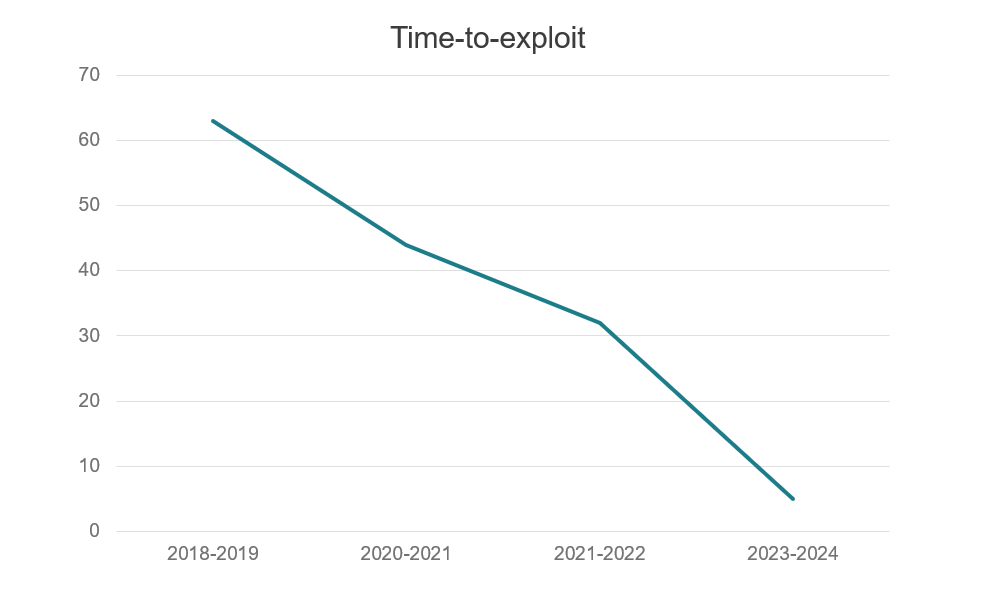
The average time-to-exploit has dropped to around five days, meaning attackers can weaponise and mass-exploit newly disclosed vulnerabilities faster than most organisations are able to patch them. Defenders must therefore act quickly when new advisories are released; waiting for the usual cycle of detection plugin updates, exposure discovery, alerting to IT, and patch deployment is often too late. Security teams and automated solutions need to work proactively with threat intelligence feeds and begin investigating possible exposures immediately after new disclosures. Even before automated scanners can detect a new vulnerability, indicators such as open ports and service banners can reveal potential exposure. A proactive approach may include temporarily disabling or isolating possibly affected assets until further investigation has been completed.
(source: Google Mandiant)
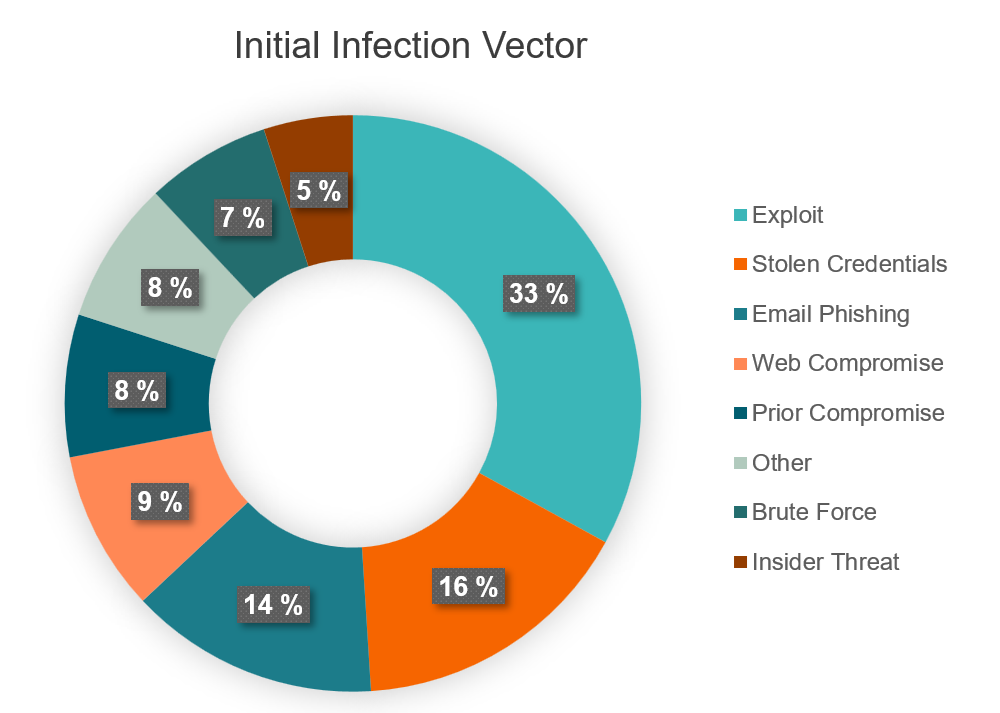
Furthermore, recent data shows that most compromises still begin with exposures that should be easily preventable with sufficient proactive cybersecurity measures. Exploitation of vulnerabilities accounts for one third of incidents, while stolen credentials and web compromise account for another 25 percent. This shows that continuous monitoring and rapid validation of new vulnerabilities, together with proactive detection of other possible exposures, remain key to reducing the risk of initial compromise.
(source: CrowdStrike, Google Mandiant)
Recommendations: moving towards a unified view of organisational risk
A unified approach to every aspect around proactive security is needed to manage risk and cyber exposures effectively now in 2026. It is not enough to rely solely on reactive detection and response capabilities. Organisations must focus on reducing their attack surface and addressing exposures before they turn into incidents. Look at it in simple terms; you would always start by locking your front door before investing in alarms and surveillance.
Put another way; it is both easier and cheaper to prevent an attack, rather than to stop one that is already happening, or in worst-case, recover from a successful one.
Achieving this requires a combination of technology, processes, and human expertise. Automated tools provide continuous visibility, but real progress depends on structured frameworks, strong governance, and collaboration between operational and strategic teams. Many organisations struggle with vulnerability fatigue caused by excessive data and alerts. A clear prioritisation model is necessary to ensure that resources are directed toward the exposures that truly matter.
Vulnerabilities and exposures
An effective exposure management program combines multiple data sources and technologies to achieve full coverage across the environment:
- Continuous Vulnerability and Asset Management is the baseline of most exposure management programs, maintaining visibility of all assets and identifying vulnerabilities across internal, external, cloud, and hybrid environments
- External Attack Surface Management enables continuous discovery, attribution and assessment of internet-facing assets to detect shadow IT, exposed services and misconfigurations that may increase external risk
- Dynamic Web Application and API Security Scanning provides ongoing and purpose-built testing of web applications and APIs to identify vulnerabilities, logic flaws and configuration weaknesses, ideally integrated into a SecDevOps process
- Cloud and Container Security Posture Management uses cloud-native solutions to detect misconfigurations, compliance gaps and insecure deployments across multi-cloud platforms and containerised environments
- Identity Exposure Management identifies excessive privileges, weak configurations and other identity-related weaknesses across Active Directory, Entra ID and other authentication systems
- OT and IoT Vulnerability Monitoring delivers specialised monitoring and assessment of operational technology and IoT systems to identify vulnerabilities and improve visibility in critical environments
- Digital Threat Monitoring provides continuous monitoring of open, deep and dark web sources to detect data leaks, domain abuse and other digital risks that may affect the organisation
- Third-Party Risk Management tracks vulnerabilities and exposures within partner, supplier and service provider ecosystems to manage external dependencies and supply-chain risk
- AI Exposure Monitoring focuses on identifying risks related to Artificial Intelligence-driven tools, generative models and exposed machine learning assets to prevent unintended data leakage or misuse
Each of these domains contributes to a unified picture of the combined organisational risk, enabling prioritised remediation and improved security posture.
Validations and "deep" prioritising
Once exposures are identified, validation activities can be used to confirm real-world exploitability as well as measuring the effectiveness of existing controls. These activities include:
- Attack Path Analysis to map and visualise possible attack routes across the systems and users of an organisation
- Automated Security Validation for fast, continuous exploit verification and better risk predictions
- Continuous Purple Teaming and Breach and Attack Simulation to evaluate mitigation controls, detection coverage, and response readiness
- Penetration Testing as a Service for easy-to-access, human-controlled testing that provides deeper verification and more comprehensive results than fully automated solutions
- Vulnerability Management as a Service for coordinated, expert-led remediation follow-up and progress tracking
Bringing Everything Together: Continuous Threat Exposure Management (CTEM)
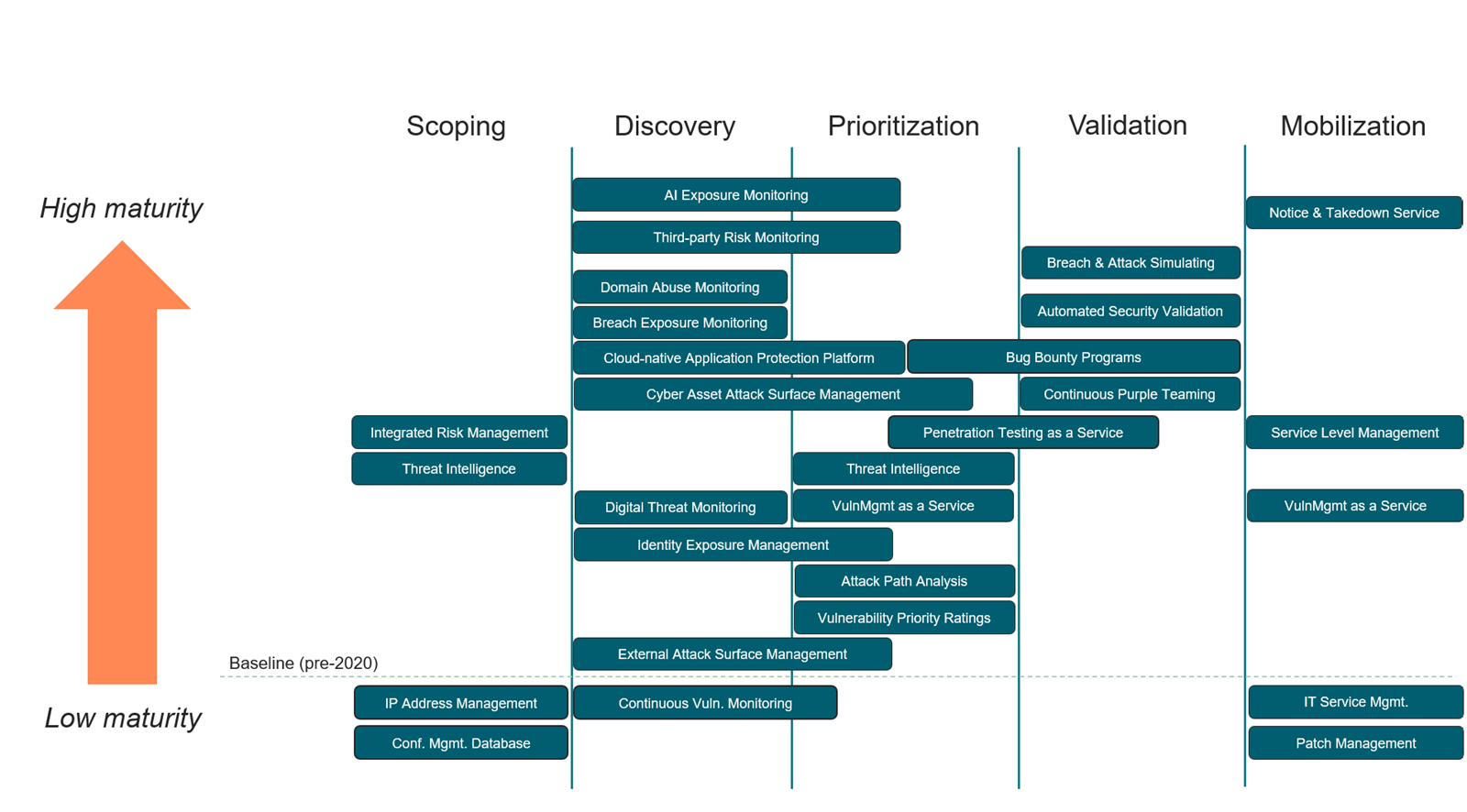
Vulnerability and exposure data often exists across multiple products and portals, while responsibility for remediation is shared between a variation of teams and third-parties. For this purpose, the Continuous Threat Exposure Management (CTEM) framework provides a structured approach for bringing every aspect of proactive cybersecurity together. This framework has many similarities to previous such systems, but stands out by having an increased focus around validation as well as a deeper emphasis on a holistic approach.
Simply put, using CTEM we can organise our approach into five iterative phases: Scoping, Discovery, Prioritisation, Validation, and Mobilisation. Besides being a modern framework for a structured exposure management process, the CTEM phases can also be used in mapping all exposure-related solutions, services and technologies within an organisation into specific target areas. This mapping reduces redundancy, increases efficiency, and ensures that efforts across exposure management, threat intelligence, and detection are coordinated toward the same objectives. The framework also helps identify capability gaps within the organisation, as well as areas where multiple overlapping solutions perform essentially the same task.
mnemonic Exposure Management Services
mnemonic’s Exposure Management Services (mEMS) provide organisations with continuous, risk-based visibility and control over their cyber exposure. These fully managed services combine advanced technology, structured processes, and deep security expertise to help identify, prioritise, and remediate vulnerabilities across modern hybrid environments.
Our services consist of four integrated areas. The first two can be tailored to fit both small, cloud-native or on-prem-only companies, as well as large multi-cloud and hybrid organisations with several thousand IT and OT assets. The latter two are designed for larger organisations with mature security programs or for companies operating critical services with a low risk tolerance. Across these services, mnemonic delivers solutions covering all the previously mentioned areas within proactive cybersecurity and threat exposure management.
- Continuous Vulnerability Monitoring (CVM): fully managed continuous monitoring across internal networks, external infrastructure, cloud environments, operational technology, IoT, identities and web applications to maintain up-to-date visibility of vulnerabilities and misconfigurations.
- External Attack Surface Management (EASM): continuous discovery, attribution and vulnerability assessments of internet-facing assets to detect shadow IT, new exposures, and vulnerable or otherwise misconfigured exposed services
- Vulnerability Management as a Service (VMaaS): a consultancy-driven service where one or more mnemonic Exposure Management team members are integrated into the organisation to assist with coordination, prioritisation, and remediation, ensuring vulnerabilities and other exposures are addressed efficiently and in line with defined service levels
- Continuous Threat Exposure Management (CTEM): an all-inclusive managed service that provides all the necessary building blocks and continuous support for implementing and operating a full CTEM framework implementation within an organisation, reducing real-world attack paths and strengthening overall resilience
All services are delivered through mnemonic's Argus platform, which consolidates data from multiple internal and third-party sources to provide a unified view of vulnerabilities, exposures, and trend metrics. The services also integrate several complementary solutions and products from leading commercial partners to enhance coverage and data quality.
mnemonic Exposure Management Services in numbers
These key metrics from 2025 illustrate the scope and operational impact of mnemonic’s Exposure Management Services, covering monitored assets, detected vulnerabilities and dedicated analyst efforts.
- Continuously monitored assets in Argus: 255,716
- Unique exposure observations added to Argus: 23,994,134
- New critical (CVSS>9.0) vulnerabilities detected: 843,714
- Median vulnerability resolution time across all severities: ~12 days
- Consultancy hours delivered across VMaaS and Exposure Management services: 8,278
By combining these capabilities, mnemonic helps organisations move from reactive patching to proactive exposure management, transforming insight into action and strengthening overall cyber resilience.
Get in touch